maintenance:general:ssh_jumphost
Table of Contents
SSH jumphost
To set up a permanent jumphost for all SSH sessions from NetYCE the following is required.
- Generate SSH keys on the netyce server
ssh-keygen -b 2048 - Copy the contents of
.ssh/id_rsa.pubto the jumphost~/.ssh/authorized_keysfile. Make sure it is all on one line. (you could use:ssh-copy-id -i ~/.ssh/id_rsa.pub <jumpuser>@<jumphost>) - Verify you can login to the jumphost without a password
ssh <jumpuser>@<jumphost> - modify the /opt/yce/etc/ssh_config to include the desired pieces:
Host jumphost Hostname 192.168.182.136 User your_user IdentityFile ~/.ssh/id_rsa Host 192.168.182.191 192.168.182.192 # you could also do: 192.168.182.* ProxyCommand ssh jumphost -W %h:%p -F /opt/yce/etc/ssh_config
- do not modify other aspects
- Verify you can connect to a node.
ssh <user>@<node> -v -F /opt/yce/etc/ssh_config- you should see this line in the debug output:
debug1: Executing proxy command: exec ssh -q -i ~/.ssh/id_rsa <jumpuser>@<jumphost> -W <node_ip>:22
From this point on all SSH session will use the jumphost.
More details on ssh_config. Please note the version of ssh, this may have limitations.
Drawbacks
NCCM
Without having direct return traffic from the node to NetYCE cripples the NCCM functionality.
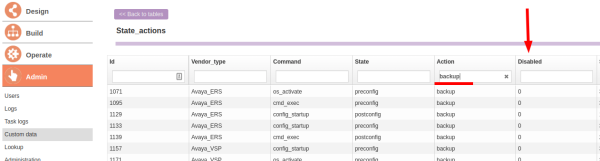
You'll have to disable the pre and post backups for the command_jobs as well.
Set all disabled values to 1.
OS upgrades
Since the NetYCE server isn't reachable from the node, the OS can't be retrieved for OS upgrades.
LDAP: couldn't connect to LDAP server
maintenance/general/ssh_jumphost.txt · Last modified: 2020/07/06 14:26 by bdorlandt